Episode Transcript
Transcripts are displayed as originally observed. Some content, including advertisements may have changed.
Use Ctrl + F to search
0:00
I'm Karl Miller, the host of the
0:02
podcast Kill List. One night, a
0:05
hacker breaks into a dark web murder
0:07
for hire site, uncovering a chilling
0:09
cache of documents called the Kill
0:11
List. It details hundreds of
0:14
names around the globe, complete with
0:16
faces, addresses, as
0:18
well as payments and instructions for their
0:20
murders. When a murder
0:22
disguised as a suicide shakes a quiet
0:25
suburb, a hacker connects the victim to
0:27
the Kill List. When local
0:29
police slow to act, he turns to
0:31
an unsuspecting investigative journalist to help. That's
0:34
me. When law enforcement
0:36
decide not to investigate, our team is
0:38
forced to take matters into our own
0:40
hands. A decision that
0:42
plunges us into a high-stakes race to
0:45
warn those whose lives are in danger.
0:48
And it turns out, convincing a total
0:50
stranger that someone wants them dead is
0:53
not easy. I'm about to play
0:55
a clip from Kill List. Remember
0:57
Kill List on the Rondry app or wherever you
0:59
get your podcasts. All
1:07
right,
1:11
you ready? Yeah. It's
1:13
a Thursday afternoon and I'm going to call with
1:15
one of my producers. The
1:17
road outside my house is almost
1:19
totally silent. On my
1:22
computer, I open Chris' document. Oh,
1:24
wow. There's a lot on here. Yeah. Chris
1:27
has run me through the orders, but this
1:29
is the first time I've got my hands
1:31
on the Kill List itself. It's
1:35
a long spreadsheet of names,
1:37
locations, telephone numbers.
1:40
So how many do we have? It looks like there's 85. On
1:44
this list. I scroll through the list. A
1:46
man from the US, a woman from Russia.
1:50
Alongside each name, there are contact details.
1:53
Service addresses, details of their movements,
1:55
and in most cases, there are
1:58
photos. The
2:00
photos are the thing that strike me
2:02
first a few dozen people staring out
2:05
at you as you open this document
2:08
In one a middle-aged man stands surrounded
2:10
by his family his light blue eyes
2:12
twinkle with a deep and joyful pride
2:14
in Another a woman tilts
2:16
her head as she smiles shyly at the
2:18
camera over rimless glasses. She's
2:20
somewhere glitzy She looks relaxed and
2:22
happy The thing that's
2:24
so striking about these photos is that they look
2:27
like they've all been taken from the social media
2:29
They look like kind of mainly Facebook profiles. So
2:31
they're they're the ones that you decide to put
2:33
on your profile picture Yeah, they're nice
2:36
photos. Yeah, and it's I
2:39
mean, it's just a photo but They
2:41
all just sort of have this on, you know, they just don't
2:43
know and this is just sort of
2:45
looming over their head And they have no idea, you know Man,
2:49
this is awful This
2:51
list looks like any other Excel
2:54
spreadsheets. It's innocuous boring even
2:57
until you read the instructions listed against
2:59
each name These
3:23
are the messages written by whoever paid to
3:25
have these people Assassinated
3:28
their specifications for the hit Can
3:31
you kidnap silent and erase without a trace
3:33
killer nurse in type a I guess we
3:35
don't know the backstory but like a nurse
3:38
I want her to be killed. They should see
3:40
she's dead because of accident Kidnap
3:43
family in Hong Kong. Can we say 15
3:45
Bitcoin for hit with a car and ensure
3:48
fatality? Mother needs to
3:50
die. Someone wants to kill their mom
3:52
killing unidentified women in Ottawa Kill a
3:54
woman who permitted sexual abuse. Mr. Lehman
3:56
45 years old Jesus,
3:59
man This is terrible. Just like these are
4:01
really possibly 85 really serious
4:03
crimes just staring back at us. Yeah.
4:06
I mean, this is conspiracy to commit murder. Ethically
4:13
this is the hardest thing
4:16
to cover that I've ever tried to do. And
4:19
for sure, I mean, this is a ethical bomb waiting
4:21
to blow up in our faces if we don't do
4:23
this correctly. Yeah, I don't know, man. It looks like
4:25
a big Pandora's box that we're
4:28
opening. And once you open it, it's open, man.
4:30
I don't think we can put it shut. The
4:34
thought of what could go wrong if I
4:36
meddle with this is terrifying. But
4:38
so is the thought of what could happen if
4:40
I do nothing. So
4:47
I start with the obvious step. I'm
4:50
quite nervous, honestly. I wasn't able to sleep that
4:52
well. I don't know why. It
4:55
suddenly makes it a lot more real. And it's just
4:57
a spreadsheet at the moment. And it's about to turn
4:59
into a crime. I'm
5:01
about to phone the police and hand over
5:04
my information. Chris
5:06
might have struggled with law enforcement, but
5:09
I've worked with the police before in my
5:11
reporting. I'm confident I can do better. After
5:14
all, this is a credible threat. How
5:17
hard can it be to get them to
5:19
take it seriously? All right. Should
5:22
I just do it then?
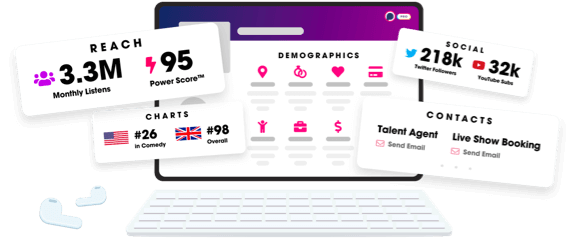
Unlock more with Podchaser Pro
- Audience Insights
- Contact Information
- Demographics
- Charts
- Sponsor History
- and More!
- Account
- Register
- Log In
- Find Friends
- Resources
- Help Center
- Blog
- API
Podchaser is the ultimate destination for podcast data, search, and discovery. Learn More
- © 2024 Podchaser, Inc.
- Privacy Policy
- Terms of Service
- Contact Us
