CPradio
A Technology podcast
Episodes of CPradio
Mark All
In the grand scheme of cybersecurity, the design issue in Foxit PDF Reader was really very minor. But it revealed a much larger and more impactful phenomenon that we’ll probably have to deal with for as long as there are computers around: the i
Once every year, Check Point releases an annual report reviewing the biggest events and trends in cybersecurity. In this episode we'll break down the latest iteration, focusing on its most important parts, to catch you up on what you need to kn
For years now, Iran’s state-sponsored hackers have been some of the most prolific in the world. But prolific does not necessarily mean sophisticated -- its attacks haven’t quite impressed in the way that the U.S., Russia, and China’s do. But in
Once a year, Check Point Research releases a “mid-year report”: a summary of the first half of the calendar year in cybersecurity, including all of the major changes, trends, and events that defined January through June. Obviously a lot happens
Between corporations, governments, and the rest of us, billions are spent every year trying to secure cyberspace. Which makes it almost unbelievable to think that just one, simple policy change from one company -- with almost no cost to anybody
For all the ridiculous spam calls in the world, but a small percentage of them are actually, legitimately, convincing. According to the Korean government, “voice phishing” compromises nearly 200 Korean citizens every day, with average financial
In July 2021, several prominent human rights activists in Azerbaijan received the same phishing email that delivered them spyware, capable of causing significant harm to their personal and professional lives. But that was only the beginning of
In 2022, government APTs wiped out entire computer systems, hackers turned good software evil, and ransomware evolved into something entirely new. In this episode we'll review the biggest stories, most important trends, and cutting insights fro
Today's AI can beat humans at Jeopardy, chess, recognizing faces and diagnosing medical conditions. As of last Fall it can write malware, too. In fact, it can write an entire attack chain: phishing emails, macros, reverse shells, you name it. W
Earlier this Fall, some users of the OpenSea trading platform posted dire messages to Twitter: all of the NFTs in their wallets were gone. Thousands of dollars worth of investments had suddenly disappeared. Soon it became clear: they were never
For decades, hacktivism has been associated with groups like Anonymous. Recently, though, something has changed. An entirely new kind of hacktivist has arisen: one with more resources, capabilities and power than anything we've seen before.
Every year, ordinary people lose money in blockchain hacks. Could it be that this technology is simply insecure by nature? Or is there something we’re all missing -- something that can save this industry, and the millions of people who’ve inves
How was the use of cyber manifested in the Russia-Ukraine war? Will Microsoft block VB macros?We'll discuss all this and more while reviewing the Mid-Year Cyber Attack Trends report of 2022.
On March 23rd, 2022, individuals working at the most important defense research institutes in Russia all received variations of the same email. The messages appeared to be quite official, regarding sanctions for Ukraine. In reality they were tr
Five years ago today, the world witnessed the most destructive ransomware attack ever. Its name was Wannacry, and it changed everything. What happened, how has ransomware evolved since, and have we learned our lesson? Or could something just li
The Conti group tallied over 700 victims, including many multi-million-dollar corporate, government and healthcare organizations. Then, in their most publicized move yet, they put their full backing behind the Russian invasion of Ukraine.One an
Did you know that in 2021 there has been a 40% increase in weekly average number of cyber attacks compared to 2020? That is just one of the fascinating findings in the report published by Check Point due to the Cybersecurity Awareness Month. In
You own some pretty "smart" computers. The laptop on your desk, the phone in your pocket, the system that runs your car. But you're also surrounded by "dumb" computers--simple machines, like your alarm clock, your computer mouse, your refrigera
It seemed like a totally normal day--people went to work, to school, to get away for an early weekend. Then, across the country of Iran, trains began to freeze in place. The system for tracking them went down. And, on display screens in station
In this episode of “Cyber Academy" we will talk about the CVE database. What's a CVE? What do the numbers attached to the CVE mean? Are they random or not? Why do we need to catalogue CVEs? What is the connection between CVEs and dictionaries,
Check Point Research (CPR) finds security flaws in Atlassian, a platform used by 180,000 customers worldwide to engineer software and manage projects. With just one click, an attacker could have used the flaws get access to the Atlassian Jira b
In this episode of "Cyber Academy" we will talk about viruses, worms and trojans. What is the difference between these three types of malware and what they have in common. We will talk about their evolvement since the early days of the internet
Last May, in one of the most brazen attacks ever attempted, cybercriminals from Eastern Europe shut down the supply of gasoline to most of the east coast of the United States. Past the many millions of people affected, and the many millions of
In this episode of “Cyber Academy, we will talk about Botnets. What are Botnets used for? How does the Botmaster, the attacker, control the bots he has under his control? We will talk about the different aspects of this modern-day crime. For ex
Would you use a computer without any kind of antivirus? Would you put your personal photos on that device? Use it to text and email? Access your bank? It turns out: you're probably already doing all of these things. The most sensitive, least pr
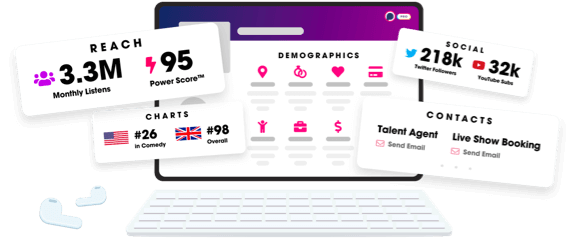
Unlock more with Podchaser Pro
- Audience Insights
- Contact Information
- Demographics
- Charts
- Sponsor History
- and More!
- Account
- Register
- Log In
- Find Friends
- Resources
- Help Center
- Blog
- API
Podchaser is the ultimate destination for podcast data, search, and discovery. Learn More
- © 2024 Podchaser, Inc.
- Privacy Policy
- Terms of Service
- Contact Us
